AI-Generated Code Audit
Make your AI-built application production-ready — fix security holes, optimize API costs, and prevent data leaks before they cost you

From AI Prototype to Production-Ready
The Problem with AI-Generated Code
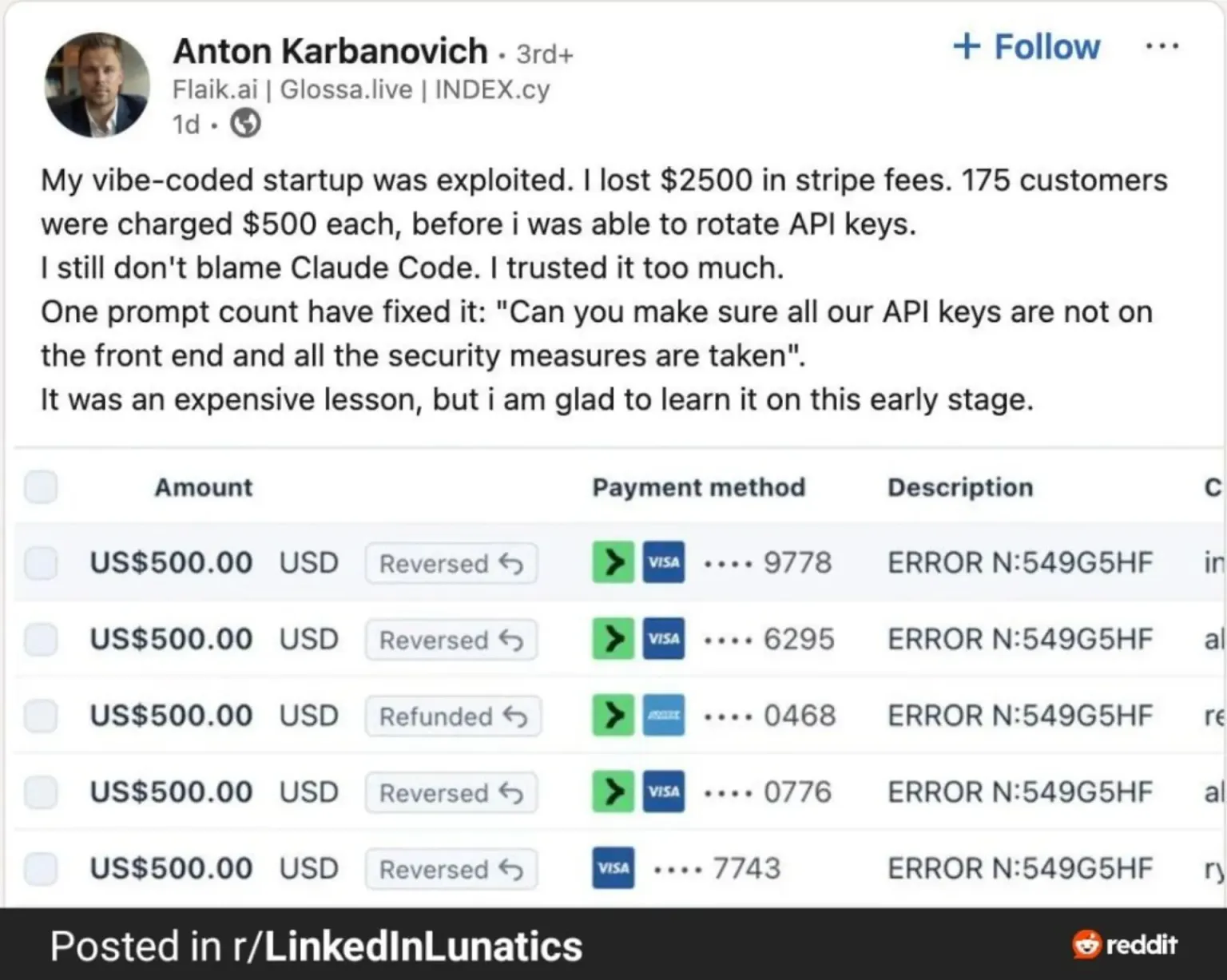
AI coding tools like Cursor, Bolt, Lovable, and ChatGPT make it possible for anyone to build a working application. The prototype looks great. It runs locally. You show it to investors or early users and get positive feedback. Then you deploy to production — and the problems begin.
AI agents write code that works, but they don't write code that's production-ready. They don't think about what happens at scale. They don't consider what an attacker would do. They don't optimize for cost. The result is an application that functions correctly in demos but bleeds money, leaks data, or breaks under real traffic.
These numbers come from independent research: Veracode tested 100+ LLMs and found 45% of generated code fails security tests. Apiiro's 2025 analysis showed AI-assisted developers expose credentials nearly twice as often. NYU researchers found ~40% of Copilot-generated programs contained vulnerabilities, while Stanford's study confirmed developers using AI assistants produce less secure code — and are more confident it's safe.
What Goes Wrong in AI-Built Applications
We've audited dozens of AI-generated codebases. The same categories of problems appear in nearly every one. These aren't edge cases — they're systematic blind spots that AI coding tools consistently miss.
Security Vulnerabilities
- Exposed API Keys and Secrets
AI tools frequently hardcode API keys, database credentials, and third-party service tokens directly in source code. These end up in public repositories, client-side bundles, or environment files that ship to production. One leaked OpenAI key can generate thousands of dollars in unauthorized usage within hours.
- Missing Authentication and Authorization
AI-generated apps often implement authentication at the surface level — a login screen exists, but the backend doesn't actually verify permissions. API endpoints accept any request. Admin routes are accessible without role checks. User A can see User B's data by changing an ID in the URL.
- Injection Attacks
SQL injection, XSS, and prompt injection are pervasive in AI-built code. AI models generate code that concatenates user input directly into queries, HTML, or LLM prompts without sanitization. A single vulnerable endpoint can compromise your entire database or allow attackers to manipulate your AI's behavior.
- Insecure Data Storage
Personal data stored in plain text, session tokens in localStorage, passwords hashed with MD5 or not hashed at all. AI tools default to the simplest implementation, which is rarely the secure one. GDPR and privacy compliance is typically absent.
API Cost Optimization
- Redundant API Calls
The most expensive problem we find. AI-generated apps make unnecessary calls to paid third-party APIs — geocoding services, financial data providers, AI models, verification APIs. They call the same endpoint multiple times for the same data, fail to cache responses, and make requests that could be avoided entirely with simple local logic. We routinely find apps where 60-80% of API spend is wasted.
- Missing Rate Limiting and Budgets
No per-user rate limits. No daily spend caps. No circuit breakers when API costs spike. A single user — or a bot — can burn through your entire monthly budget in a day. AI tools never implement cost controls because they have no concept of your business model or the pricing tiers of the services you integrate.
- No Caching or Batching
Fetching the same exchange rate, IP geolocation, or user profile from a paid API on every single request instead of caching it. Making individual API calls in a loop instead of using batch endpoints. Each unnecessary request costs money, and at scale these add up to thousands of dollars per month.
Data Leaks and Privacy
- Logging Sensitive Information
AI-generated code loves verbose logging. User emails, passwords, payment details, and personal data end up in application logs, error tracking services, and third-party analytics. These logs are often accessible without authentication and retained indefinitely.
- Oversharing Through APIs
API responses that return entire user objects — including hashed passwords, internal IDs, email addresses, and metadata — when the frontend only needs a display name. GraphQL endpoints without depth limits that allow attackers to extract your entire data model.
- Third-Party Data Exposure
AI tools integrate analytics, error tracking, and monitoring services without considering what data flows to them. User behavior, personal information, and business data end up in third-party systems without consent, violating GDPR and other privacy regulations.
What Our Audit Covers
Security Vulnerability Scan
OWASP Top 10, injection attacks, authentication bypass, secrets exposure
API Cost Analysis
Paid API usage audit, redundant calls, caching opportunities, spend projections
Data Leak Detection
Log analysis, API response audit, third-party data flow mapping
Performance Review
Database queries, N+1 problems, memory leaks, load capacity
Infrastructure Audit
Deployment config, environment isolation, backup and recovery
Compliance Check
GDPR readiness, data retention policies, consent mechanisms
Our Audit Process
We deliver a complete audit with actionable fixes — not just a list of problems.
How It Works
- Codebase Access and Scope
You grant us read access to your repository and deployed environment. We define the audit scope based on your priorities: full audit or focused on specific areas (security, costs, or data privacy). No changes are made to your code during the audit phase.
- Automated Analysis
We run static analysis, dependency vulnerability scans, secrets detection, and API cost profiling against your codebase. This catches the low-hanging fruit — known vulnerabilities, exposed credentials, outdated packages with security patches, and obvious performance issues.
- Manual Expert Review
Our engineers manually review the architecture, business logic, authentication flows, API integrations, and data handling. This is where we find the problems that automated tools miss: logic flaws, authorization gaps, cost optimization opportunities, and design issues that will cause problems at scale.
- Report and Prioritization
We deliver a detailed report with every finding categorized by severity (critical, high, medium, low) and type (security, cost, privacy, performance). Each finding includes a clear explanation of the risk, proof of concept where applicable, and a specific fix recommendation with code examples.
- Fix Implementation
Optionally, we implement the fixes ourselves. Critical security patches are applied first, followed by cost optimizations and privacy improvements. You review every change before it's merged. The result is a production-ready codebase you can deploy with confidence.
AI-Generated Code vs Production-Ready Code
What changes when your codebase goes through a professional audit
| Aspect | After AuditProduction-Ready | AI-Generated Code | Built from Scratch |
|---|---|---|---|
| Security | Hardened | Surface-Level | Varies by Team |
| API Costs | Optimized | 5-20x Overspend | Usually Optimized |
| Data Privacy | GDPR-Compliant | Data Leaks Common | Depends on Process |
| Time to Production | 2-4 Weeks | Already Running | 3-6 Months |
| Cost to Launch | Low (Audit Fee) | Free (Risky) | High (Full Dev) |
| Error Handling | Graceful Recovery | Crashes in Edge Cases | Usually Handled |
| Scalability | Load-Tested | Untested | Architected for Scale |
| Monitoring | Full Observability | None or Excessive | Standard Setup |
The bottom line: AI-generated code gets you 80% of the way there in 5% of the time. But that last 20% — security, cost optimization, data privacy, error handling — is what separates a demo from a production application. An audit bridges the gap without throwing away your AI-built foundation.
AI-Generated Code Audit Pricing
Transparent pricing based on your codebase size and audit scope
Security Focused
Critical vulnerabilities only
1-2 weeks
- OWASP Top 10 vulnerability scan
- Secrets and credentials detection
- Authentication & authorization review
- Dependency vulnerability check
- Prioritized findings report
- Fix recommendations with code examples
Cost Optimization
Reduce your API spend
1-2 weeks
- Paid API usage profiling
- Redundant call identification
- Caching & batching strategy design
- Rate limiting implementation plan
- Per-request cost optimization
- Projected monthly savings report
Full Audit
Complete production readiness
2-4 weeks
- Everything in Security Focused
- Everything in Cost Optimization
- Data privacy & GDPR review
- Performance & scalability analysis
- Infrastructure audit
- Detailed report + fix implementation
Ongoing Support
Continuous audit & monitoring
per month
- Monthly security scans
- API cost monitoring & alerts
- Dependency update reviews
- New feature security review
- Priority incident response
- Direct Slack/Telegram access
Custom Pricing Available
Pricing depends on codebase size, number of services and integrations, and audit scope. A small single-service app with one AI integration will be at the lower end. A multi-service platform with several AI providers, payment processing, and user data will require a more thorough review. Contact us for a free initial assessment.
Frequently Asked Questions
Common questions about auditing AI-generated code
Yes. We audit code regardless of how it was generated. Whether you used Cursor, Bolt, Lovable, Claude, ChatGPT, GitHub Copilot, or any combination of AI tools, the audit process is the same. The output is code, and that is what we review. We have experience with all major AI coding tools and know their common failure patterns.
Ready to Make Your AI-Built App Production-Ready?
Let's audit your codebase and turn your AI prototype into a secure, cost-efficient application you can confidently deploy.